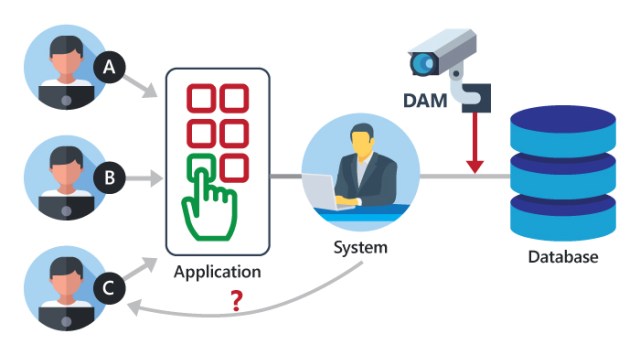
Database Activity Monitoring & Database Firewall
Databases contain sensitive and proprietary information, making them a prized target for cybercriminals who are constantly looking for ways to access valuable data for large financial payoffs.
As any company knows, the information stored within a database is what every hacker is hoping to get their hands on.
According to the most recent Threat Landscape, Ransomware is the No 1 type of malware costing companies millions of dollars in revenue including the downtime involved in restoration of data.
Common Threats
and Challenges
Many software misconfigurations, vulnerabilities, or patterns of carelessness or misuse can result in breaches. The following are among the most common types or causes of database security attacks and their causes.
1) Insider threats: An insider threat is a security threat from any one of three sources with privileged access to the database:
- A malicious insider who intends to do harm
- A negligent insider who makes errors that make the database vulnerable to attack
- An infiltrator—an outsider who somehow obtains credentials via a scheme such as phishing or by gaining access to the credential database itself nsider threats are among the most common causes of database security breaches and are often the result of allowing too many employees to hold privileged user access credentials.
2) Human error: Accidents, weak passwords, password sharing, and other unwise or uninformed user behaviors continue to be the cause of nearly half (49%) of all reported data breaches.(Link resides outside IBM)
3) Exploitation of database software vulnerabilities: Hackers make their living by finding and targeting vulnerabilities in all kinds of software, including database management software. All major commercial database software vendors and open source database management platforms issue regular security patches to address these vulnerabilities, but failure to apply these patches in a timely fashion can increase your exposure.
4) SQL/NoSQL injection attacks: A database-specific threat, these involve the insertion of arbitrary SQL or non-SQL attack strings into database queries served by web applications or HTTP headers. Organizations that don’t follow secure web application coding practices and perform regular vulnerability testing are open to these attacks.
5) Buffer overflow exploitations: Buffer overflow occurs when a process attempts to write more data to a fixed-length block of memory than it is allowed to hold. Attackers may use the excess data, stored in adjacent memory addresses, as a foundation from which to launch attacks.
6) Denial of service (DoS/DDoS) attacks: In a denial of service (DoS) attack, the attacker deluges the target server—in this case the database server—with so many requests that the server can no longer fulfill legitimate requests from actual users, and, in many cases, the server becomes unstable or crashes
Request more details below..

